Fundamentals of NaC with Nexus Dashboard
This document is an important component of this guide, as it provides a foundational understanding of the structure of the code. Understanding how Ansible is structured and utilizing various Ansible collections, is important to effectively use the Network as Code (NaC) capabilities with Nexus Dashboard.
Ansible Collections
Section titled “Ansible Collections”Ansible collections are a way to package and distribute Ansible content, including roles, modules, and plugins. They allow for better organization and sharing of Ansible code. In the context of Network as Code with Nexus Dashboard, collections are used to encapsulate the necessary components for managing network configurations.
The solution is built on top of the ND Ansible collection. This collection is built by the Cisco PIE (Platform Independent Engineering) team. For all capabilities that we build on NaC VXLAN ND, the capability must exist in the underlying collection, otherwise a REST fallback module must be used.
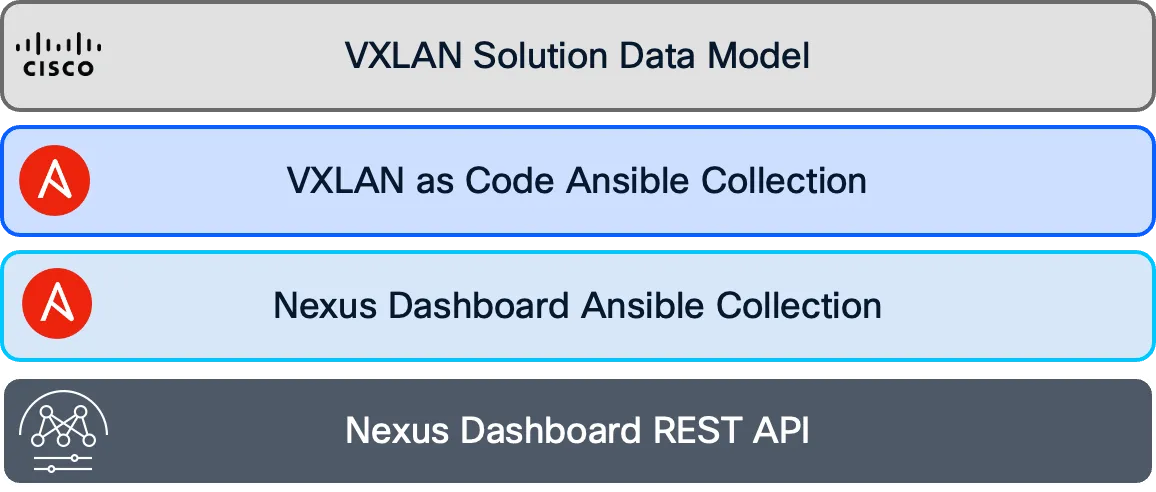
In the following chart you can see the overall software architecture.
Ansible Roles
Section titled “Ansible Roles”Ansible roles are a way to organize Ansible tasks, handlers, variables and other components into reusable units. Roles outside the context of Network as Code are powerful to separate data and logic. When a role is initialized, Ansible creates a specific data structure that contains:
tasksdirectory for defining the tasks to be executed.handlersdirectory for defining handlers that can be triggered by tasks.varsdirectory for defining variables used by the role.defaultsdirectory for defining default variables that can be overridden.filesdirectory for storing static files that can be used by tasks.templatesdirectory for storing Jinja2 templates that can be rendered with variables.metadirectory for defining metadata about the role, such as dependencies on other roles.librarydirectory for defining custom modules.
In the context of Network as Code with Nexus Dashboard, roles are used to define specific tasks and workflows for managing VXLAN EVPN fabrics. These are the Validate Role, Create Role, Deploy Role, and Remove Role.
Validate Role
Section titled “Validate Role”The validate role ensures that the data model is correct and that the data model can be processed by the subsequent roles. The validate role reads all the files in the host_vars directory and creates a single data model in memory for execution.
As part of the VXLAN as Code service from Cisco, you will also be able to utilize the semantic validation feature to make sure that the data model matches the intended expected values. This is a powerful feature that allows you to ensure that the data model is correct before it is deployed to the network. Additionally, the validate role allows creation of rules that can be used to prevent operators from making specific configurations that are not allowed in the network. These can be as simple as enforcing proper naming conventions to more complex rules for interconnectivity issues that should be avoided. These rules are coded in Python and can be constructed as part of the Services as Code offer.
Create Role
Section titled “Create Role”The create role builds all of the templates and variable parameters required to deploy the VXLAN fabric and creates fabric state in ND. The data model is converted into the proper templates required by the Ansible modules used to configure the ND controller and manage the fabric state. The create role has a dependency on the validate role.
Deploy Role
Section titled “Deploy Role”The deploy role deploys the fabric state created using the create role to the ND managed devices. The deploy role has a dependency on the validate role. Today, VXLAN as Code supports the fabric-wide deployment option with switch-level deployment being scoped for support.
Remove Role
Section titled “Remove Role”The remove role removes state from the ND controller and the devices managed by the ND controller. When the collection discovers managed state in ND that is not defined in the data model it gets removed by this role. For this reason this role requires the following variables to be set to true under the group_vars directory. This avoids accidental removal of configuration from ND that might impact the network. The remove role has a dependency on the validate role and is not enabled by default in the example repository that we are sharing.